How to Share AWS S3 Files and Folders with External Users Using NirvaShare
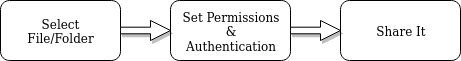
Sharing files or folders from AWS S3 with external users is a common use case across many industries. However, managing such access can present challenges, particularly around security, authentication, and authorization. NirvaShare simplifies this process by enabling secure file sharing with just a few clicks. In this document, we will walk through how to configure NirvaShare with AWS S3 storage and share files with external users using a simple Form-based authentication.
Installation
To securely share files using NirvaShare, you must first install the software in your system environment. This can be done either manually or through a marketplace. Installation links are provided below.
Storage Configuration
The next step is to configure the storage, which can be done using one of two available methods.
Login Profile for Form based Authentication
To enable secure file sharing, this step explains how to create a simple Form-based login profile, allowing you to share files or folders with password protection. You can follow the link below for detailed instructions.
Shares
At this stage, you can begin sharing files or folders. To do so, you need to create a new Share and enable Form-based authentication. Refer to the document below for guidance on creating a Share from your storage. When setting up the Share, make sure to select the login profile you created in the previous step. This login profile can be reused to create multiple Shares.
Verification
- Copy the shareable link from the “Shares” section in the NirvaShare Admin Console.
- Open the link in a browser tab—this will redirect you to the Form-based authentication login page.
- After successful authentication, you will be able to access the Shares assigned to the selected login profile.
