Search Documentation
< All Topics
Setup IAM Identity Center for Admin Console
Admin Console of NirvaShare comes with default in-built user store to support multiple admin users. It is also possible to configure Admin Console to use external Identity providers like IAM Identity Center, Active Directory, etc. In this document, we will configure Admin Console to use IAM Identity Center, so that users from IAM Identity Center will be able to login to Admin Console using SAML 2.0.
Prerequisites
As prerequisites you will need to have:
- NirvaShare installed either on cloud or on premise. You can also directly install from AWS Marketplace.
- Configure the Storage and User Application URL . For details check HERE
- Make sure proper domain name and SSL certificate is configured for Admin Console.
- You will require access to your IAM Identity Center as console administrator.
Configuration
- Login to Admin Console and click on Users & Roles tab.
- Create a new delegated admin user and select the role as super admin. Here the username must be unique and the same username should also exist in IAM Identity Center as well (can be created later too).
- In the SSH to Linux terminal where NirvaShare is installed, create a file with the below path and filename as root user.
/var/nirvashare/config.properties- Add the following entries in to the file.
ns_external_idp=true
ns_auto_create_user=true
ns_saml2_sp_company_name= <Your company name>
ns_saml2_sp_email=<your contact email id>
ns_saml2_sp_domain_url=https://<adminconsole domain name>
ns_saml2_idp_metadata_content=
- Make sure you replace with proper values for attribute names.
ns_saml2_sp_company_name
ns_saml2_sp_email
ns_saml2_sp_domain_url - Open the admin console URL https://<Your AdminConsole Domain>/saml/0/metadata
- This will display the XML metadata. Save this content into a local file system with file name as admin-console-metatdata.xml. This file will be required in later steps to configure SSO.
- Login to AWS Console as administrator.
- Go to IAM Identity Center service.
- Click on Users.
- Create a new user and make sure the username is the same as the one we created in NirvaShare AdminConsole at the beginning of the steps.
- Click on Applications from the left menu.
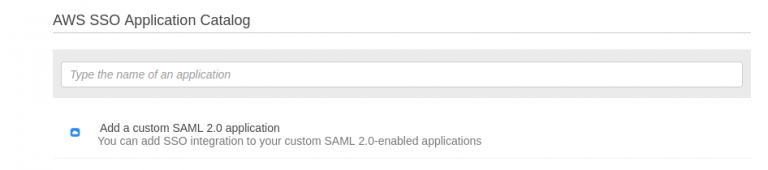
- Click on Add New Application in the top menu.
- Click on Add a custom SAML 2.0 application.
- Provide a name for the app as NirvaShare Admin.
- On the Application metadata section, browse and upload the file admin-console-metadata.xml that was obtained earlier.
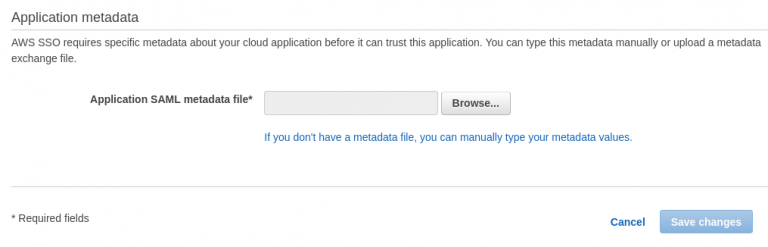
- Click on Save Changes.
- This will create a new SAML Application.
- From the IAM Identity Center metadata section, click on the download link to get the SSO metadata file. Save this file in to local file system with filename as aws-admin-metadata.xml
- Click on Attribute mappings tab and provide the value as ${user:subject} for Subject attribute.
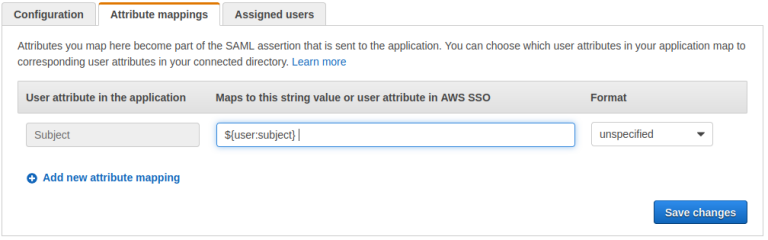
- Click on the Assigned users tab and select the user that we created in earlier steps and assign it.
- Please note that, you can also use a group and assign multiple users to it. For now, we will deal with one user.
- Next, copy paste the content of the file aws-admin-metadata.xml into a textpad. Remove new lines and disable word wrap.Make the entire content as a single line. We will need this single line metadata content in the adminConsole configuration in next steps.
- SSH to Linux terminal where NirvaShare is installed, edit the below configuration file.
/var/nirvashare/config.properties- Copy paste the metadata single line content from above steps in to this file for the attribute value of ns_saml2_idp_metadata_content.
- Save the config.properties.
- Restart adminConsole service using below command.
docker restart nirvashare_adminNow open AdminConsole https://, this will redirect to AWS and perform SSO for authentication. Reach out to our support in case you require any help or assistance.
Table of Contents
